Identify security gaps, ensure compliance readiness, and gain insight into third-party integrations on your website.
Misconfigured cloud environments and unmanaged third-party integrations can expose your infrastructure to security risks and non-compliance with key industry standards. Our tools provide insights into your environment, helping you secure your setup and maintain trust with your users.
Empower your business with a fortified infrastructure by addressing vulnerabilities, improving standards, and building trust in your digital ecosystem.
Proactively uncover and resolve misconfigurations in your cloud and infrastructure to close security gaps before they can be exploited, ensuring robust protection.
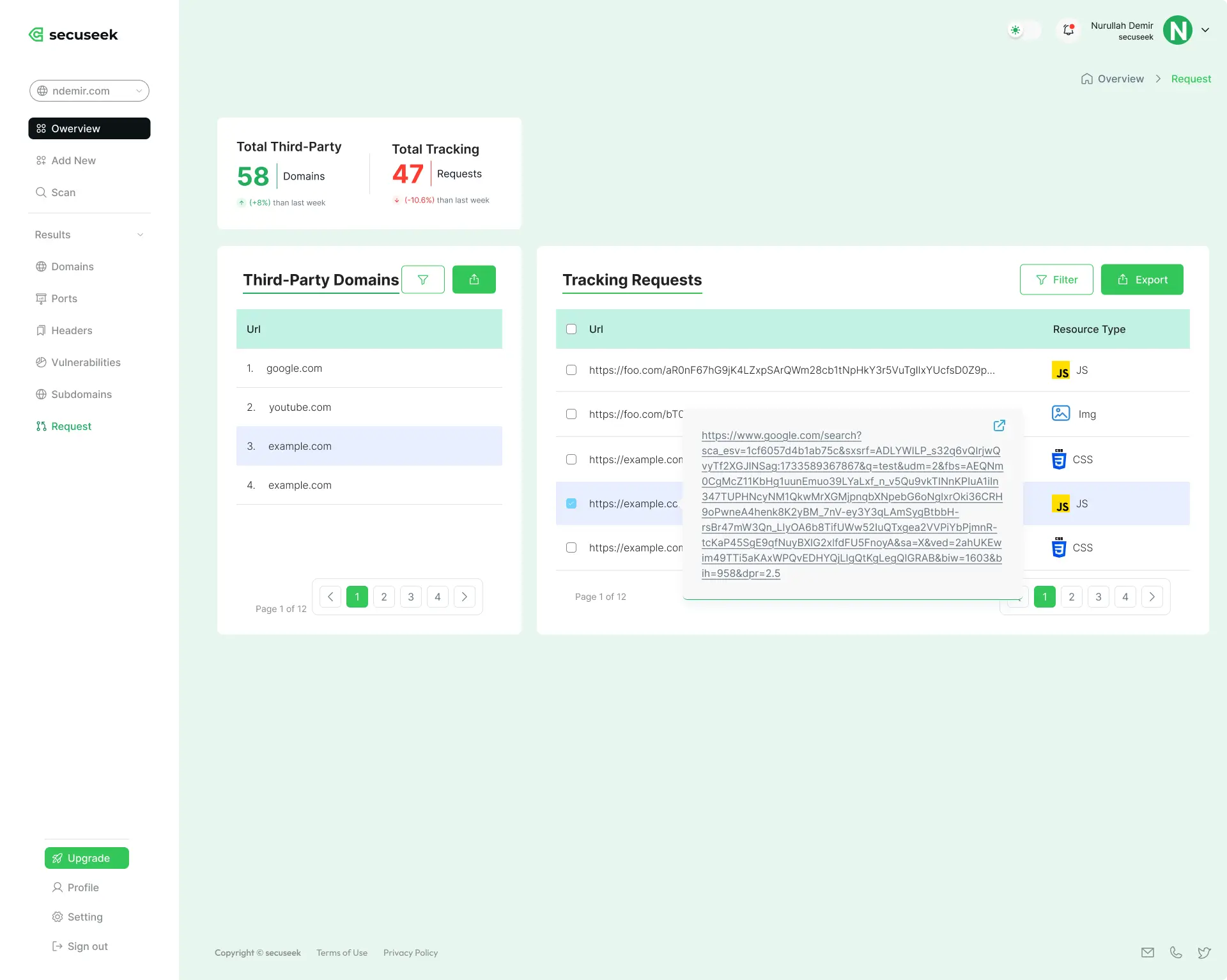
Gain complete visibility into third-party trackers and integrations, allowing you to assess and mitigate potential risks posed by external partners or services.
Align your infrastructure with industry best practices and compliance frameworks, enhancing overall resilience and regulatory readiness.
We assess your cloud environment to identify misconfigurations, such as overly permissive access controls or unencrypted data. Receive clear, actionable recommendations to close these security gaps.
Gain an overview of third-party trackers and integrations present on your website. We help you evaluate how these elements align with security best practices and industry standards like GDPR, CCPA, and PCI DSS.


Our system evaluates your website and all subdomains for vulnerabilities, malicious links, and exposed secrets.
We cross-reference requests, URLs, and IPs with trusted threat intelligence databases, including URLhaus and Phishing.Database.
You’ll receive a detailed report highlighting risks and prioritized recommendations to strengthen your security.
Prevent vulnerabilities from turning into threats.
Take control of your web security with SecuSeek.