Discover hidden risks, protect sensitive resources, and safeguard your subdomains with ease.
Unmapped subdomains, abandoned resources, and exposed files can serve as easy targets for cyberattacks. Without visibility into these assets, attackers can exploit blind spots, leading to data breaches, resource takeovers, or unauthorized access.
Protect and enhance your business with comprehensive security measures designed to safeguard your digital presence.
Secure every subdomain and resource to prevent overlooked vulnerabilities and maintain full protection of your digital assets.
Identify and mitigate risks to reduce your website’s attack surface, protecting sensitive data and minimizing potential breaches.
A secure website fosters credibility, enhances user confidence, and strengthens your brand’s reputation.
Gain complete visibility of all subdomains tied to your domain. Identify and secure blind spots before they become vulnerabilities.
Prevent attackers from hijacking abandoned or misconfigured resources, including subdomains and cloud assets.
Identify sensitive paths, such as admin pages and configuration files, that should remain private. Secure them before attackers exploit these openings.


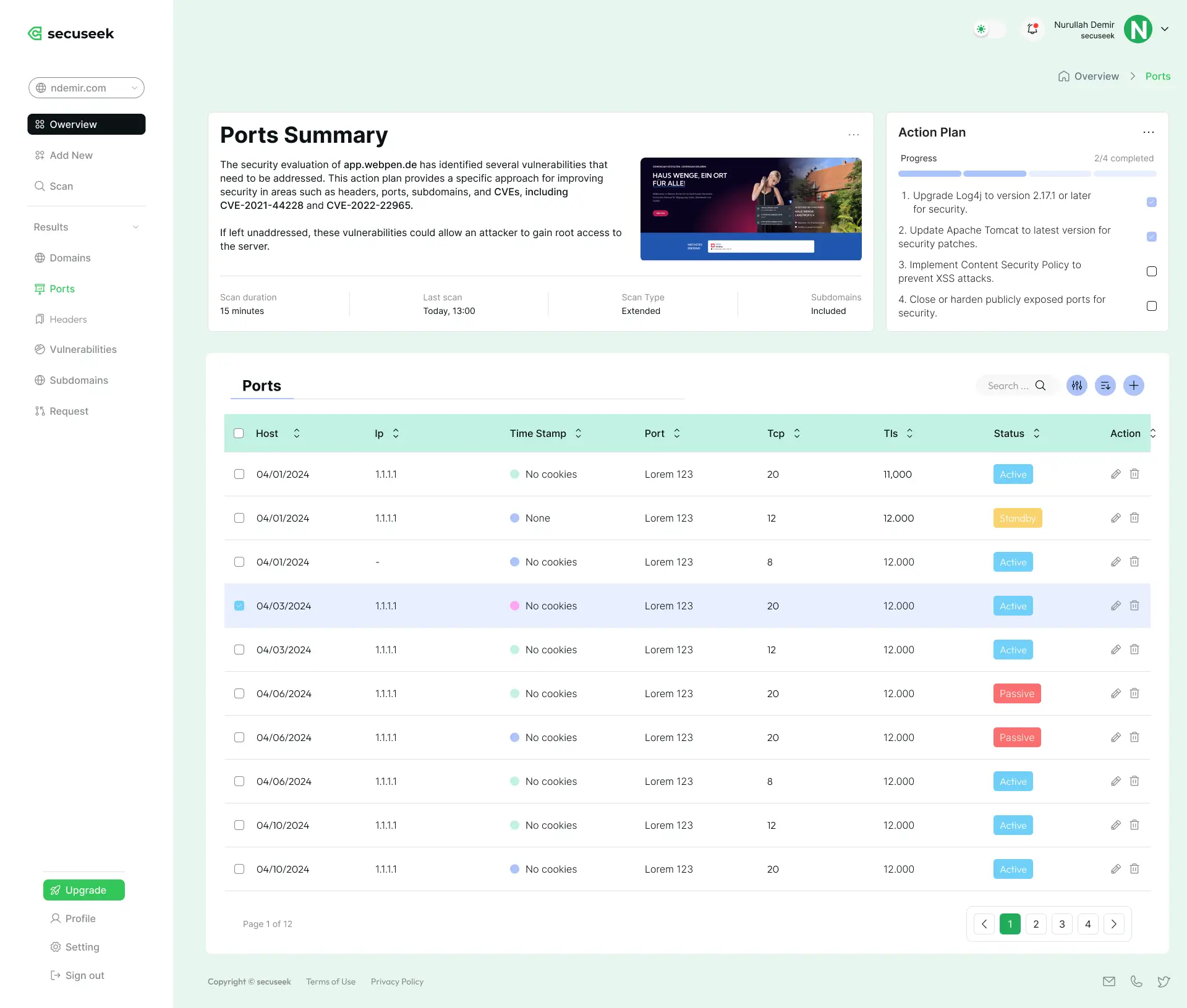
Our system evaluates your website and all subdomains for vulnerabilities, malicious links, and exposed secrets.
We cross-reference requests, URLs, and IPs with trusted threat intelligence databases, including URLhaus and Phishing.Database.
You’ll receive a detailed report highlighting risks and prioritized recommendations to strengthen your security.
Prevent vulnerabilities from turning into threats.
Take control of your web security with SecuSeek.